Latest Posts
-
Adding FreeBSD Users With Ansible
It’s Not Rocket Science
-
RADIUS Log GROK
Sprechen Sie RADIUS?
-
Defense By Proxy
Defense In Depth
-
Postfix Header Checks
-
Postfix Recipient Verification
Don’t Talk About Exchange
-
Exchange 0Day IOCs
Enemy At The Gates
-
Event Log Noise
NOBODY Did It
-
The Great MalDoc Plague
Slipping Past The Guards
-
GROK Pattern for Cisco ASA 106020
These Aren’t The Logs You’re Looking For
-
Cisco ASA Central Logging with Graylog
Kill The Noise
-
PCI Diaries 1
Put A Little Log In Your Life
-
GROK Pattern for Cisco ASA 313005
%ASA-4-313005
-
Snort Performance Profiling
My Life With Porkchop
-
Kerberoasting Countermeasures
An attacker has established a beachhead on your network compromising a low-privilege account. Privilege escalation and lateral movement are key next steps and Kerberoasting can be a low-risk/high-reward technique.
-
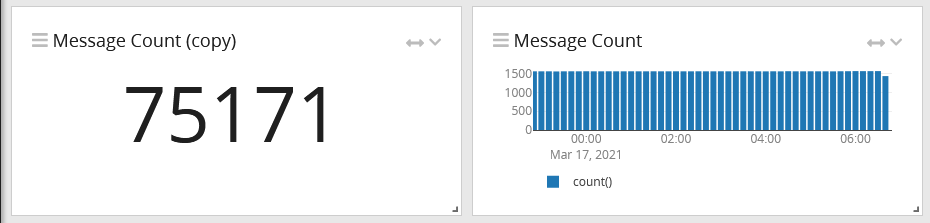
Dshield Honeypot Tricks 1
ISC SANS has a fantastic little honeypot you can throw on a Raspberry Pi. While you can interact with the collected Intel to some degree from the various dashboards on the SANS site, I wanted a bit more detail and immediate access to the logs.